Just because the good guys have discovered a new security risk doesn’t mean the bad guys haven’t known about it forever. The risk is only new to us. It’s actually been there for a long time, maybe forever. Who knows how long everyone from the black hats in Moscow to the NSA in bucolic Maryland have been taking advantage of what appears to us to be a “new” exploit?
The USB security hole recently unveiled by Berlin based Security Research Labs (SRL) seems to be of those that’s been around “forever.”
(click to enlarge)
The trouble is, most of these chips are relatively easy to reprogram.
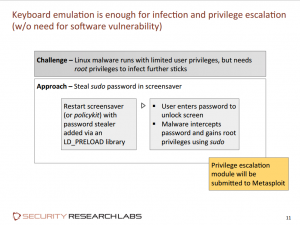
An article published yesterday on the BBC’s website, illustrated how this exploit can be used to hijack a computer:
“In one demo, shown off at the Black Hat hackers conference in Las Vegas, a standard USB drive was inserted into a normal computer.
“Malicious code implanted on the stick tricked the machine into thinking a keyboard had been plugged in.
“After just a few moments, the ‘keyboard’ began typing in commands – and instructed the computer to download a malicious program from the internet.”
In another demonstration for the BBC, a researcher with SRL, Karsten Nohl, was able to use the exploit to create a fake version of the PayPal website to steal log-in credentials.
“Unlike other similar attacks, where simply looking at the web address can give away a scam website, there were no visible clues that a user was under threat.
“The same demo could have been carried out on any website, Mr Nohl stressed.”
According to an article on the SRL website, little can be done to protect against such an attack at this time. Also, cleaning up after such an attack may be next to impossible.
“No effective defenses from USB attacks are known. Malware scanners cannot access the firmware running on USB devices. USB firewalls that block certain device classes do not (yet) exist. And behavioral detection is difficult, since a BadUSB device’s behavior when it changes its persona looks as though a user has simply plugged in a new device.
“To make matters worse, cleanup after an incident is hard: Simply reinstalling the operating system – the standard response to otherwise ineradicable malware – does not address BadUSB infections at their root. The USB thumb drive, from which the operating system is reinstalled, may already be infected, as may the hardwired webcam or other USB components inside the computer. A BadUSB device may even have replaced the computer’s BIOS – again by emulating a keyboard and unlocking a hidden file on the USB thumb drive.
“Once infected, computers and their USB peripherals can never be trusted again.”
Sean Michael Kerner writing on eWeek, downplayed these warnings:
“A reprogrammed USB device can have certain privileges that give it access to do things it should not be able to do, but the bottom line is about trust. On a typical Windows system, USB devices are driven by drivers that are more often than not signed by software vendors. If a warning pops up on a user’s screen to install a driver, or that an unsigned driver is present, that should be a cause for concern.
“As a matter of best practice, don’t plug unknown USB devices into your computing equipment. It’s just common sense, much like users should not open attachments that look suspicious or click on unknown links.”
That’s great for those tied to Windows, but doesn’t offer much help to those using Linux or OS X. As for the call for users to use good computer hygiene, most of us are doing that anyway — it’s not like this is the first security risk that’s arisen around the USB port.
For the time being, being careful might be enough, but probably not for long. Although the people at SRL are not yet releasing their modified USB controller firmwares, it’s only a matter of time before the black hats figure it out, now that the existence of the bug has been made public. So far, the USB Working Party, the organization behind the USB standard, is not commenting specifically about this exploit but is pointing to additional USB security measures that OEMs can choose to use. Hopefully, however, they’re frantically working behind the scenes to find a way to nullify this threat.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux








I’m assuming that MOST if not ALL Linux users have a modicum of sense when it comes ot security and their PC’s….like…never take a USB from someone else and insert it into your home PC without scanning it FIRST!….regardless if it came from a friend or relative…or co-worker. If you treat your machines like you’re holding the secrets to the universe on them…..you’ll probably have a better sense of control regarding your machine.
What if all periphial devices had access only through the wireless router, each having their on ip address? Just like wireless printers. That would do away with usb devices and most routers have 1 gibit wireless access anyway
Here is my plan of action. download Gparted/Parted magic, make a boot able live disk, Boot the system up from the live disk, insert the USB drive in the usb port, delete the partition make a new partition format it, bingo now it’s clean ready for use.
You misunderstand this issue. The problem is in the USB controller chip in all USB devices (thumbdrive, webcam, printer, keyboard, mouse, etc….). They are not protected and they can be rewritten i.e. infected. This is why this vulnerability is bad.
Eddie
Antivirus do not currently have the capability to scan firmware (chipset).
Harry, running USB peripherals through the router is a bad idea. Instead of infecting one computer, you infect your router, which controls your internet connection. Someone could then redirect where you go on the internet and you would not even know it, since your computer would not be infected and there are currently no AV solution to scan routers (not that it would help in this case anyway).
Carling
You can reformat and repartition your thunbdrive all you want, it will have no bearing as the chipset is still compromised and will just recompromise your drive, your computer, etc…
This is a very serious problem because if this type of malware infects you, there are currently no way to detect it. Just think how many peripherals exist that connect to a usb port.
@Carling that is the problem. It is the firmware on the device that is reprogrammed, no amount of reformatting it will change that. You *can’t* really do anything about that either. That is the issue. It is next to impossible to reset one of these devices to their original benign state.
We need sort of a USB firewall that can be on or off. It would confirm the device type when a new device is plugged in and offer a test mode for keyboard to see if they are entering commands. Hey the USB security program says my camera is a keyboard running wget malware.ru….
If my usb thumb drive is infected and says it is a keyboard instead of a flash drive, what happens when I plug in my usb drive and I cannot mount the “disk drive” because it saays it is a “keyboard”?
Wouldn’t I immediately know something was wrong, even if it was too late?
so what does it take to reprogram a device?
if we can reprogram devices as a defensive measure, this would at least allow us to secure devices that we buy for our own use by programming them with known good firmware code.
greetings, eMBee.
Maybe a simple checksum on USB devices could be implemented. MFG’s would need to get on board but it would be simple to implement.
A noisy popup could also be somewhat helpful, “you’ve plugged in a ________” click OK to accept.
Exactly Swiftnet but USB devices identify themselves by type so we don’t need a checksum. For just about every device but keyboard there is nothing they can do to interact with the system directly I guess a block device can manipulate files. So a prompt that tells you which kind of device you plugged in would go a long way.
If you read the original article, this goes beyond the fake keyboard issue. Devices can spoof network settings, act as network cards and worse.
Here are some reasons why this is very bad:
First: The device’s firmware is hostile, not files on it, so reformatting a USB drive would not make it safe.
Second: USB Drives can insert code at boot time, invisible to the OS like a BIOS based rootkit.
Third: Current anti-virus and malware scanners can’t detect this threat.
Fourth: There is the real possibility of drives being compromised en masse at the manufacturer, so being careful about which devices you use may offer little protection. Remember years ago when malware was finding it’s way onto USB based digital picture frames at the factory?
Fifth: Although not metnioned in the article, I can imagine a hostile device being programmed to compromise other USB controllers in a system, meaning it could permanently infect any computer it comes into contact with and spread to all other periperals, even if the original device is no longer present.
Put them all together and it is very scary indeed.
Steph you maybe misunderstood, I proposed to make usb devices into a device that talks directly to a router, maybe as a guest or something like that, each device needs then a pass phrase to be connected. One could still use a usb connector, but only to power the device. The mouse could still be a wireless mouse but instead connecting through a usb port route it.:)
@Harry
That really isn’t feasible. Making each and every peripheral its own host on a network is too complicated to work. Every device would need its own network stack and associated hardware driving up cost and complexity. Coordinating communications would be a nightmare. Imagine a single wireless network with a dozen or so PC’s, keyboards, and mice, as well as a few printers and scanners, handfuls of external hard drives and flash drives, etc. How do you connect the correct device to the correct PC?
I don’t think anyone would appreciate mouse lag due to wireless congestion…and the first time your wireless hiccups? Heaven help you if you need to reconfigure your wireless network.
@Patrick
Actually, any USB device can be more than one USB device at the same time. In other words, when you plug in a USB drive it can be a USB drive and a USB keyboard both. You’re system would show an additional keyboard attached if you bothered to look to see whether an additional keyboard had been attached, but that’s not something most users would automatically do.
The first attachment to a Windows machine of a new type of keyboard would show a couple of installation messages in the tray, but if the type of keyboard it claimed to be had been attached in the past, you’d get no messages.
Wow, I can’t believe I accidentally stuck a “you’re” in where it should have been just “your.”
Sean Michael Kerner: “.. don’t plug unknown USB devices into your computing equipment.”
Well, thank you captain obvious. I’ve had to support Windows users over the years. And by their own nature, they should be more concerned with what THEY are plugging THEIR USB devices into. I have 25 years of experience in Windows. And 15 years in Unix and Linux. What I suggested should be good practice for any OS out there.
– Cao
Most of us here have at some point reprogrammed hardware — whether through school, hobby, or profession.
There has always been the underlying threat that individual pieces of hardware could be subverted somehow (pick any Mission Impossible type scenario) into hijacking your computer (and through your computer, who knows what). We have just avoided thinking about it.
This just showcases another unprotected vector of attack. Like a malicious device driver, or malicious app, malicious BIOS, or malicious kernel. Fundamentally, we are assuming our systems are secure when in fact they are not secure. They just haven’t been targeted yet.
Whether the threat is malicious individual devices, or entire batches of memory sticks doesn’t really matter. Our OS’s do not police against malicious devices. And until they do we are not safe.