I shouldn’t have to say this, but child pornographers and users of child porn are scum and deserve just about any sentence meted out to them. This absolutely doesn’t mean, however, that we willy-nilly throw their rights out the window in order to catch them. Remember, in the United States we still claim to believe in the concept of “innocent until proven guilty.” If they forgot to teach you that in school, Google it. Try “Bill of Rights” as your search term.
With that out of the way, let’s get into our story…
 It appears more and more that the malware caper discovered this weekend on the TOR network was all about harvesting MAC (media access control) addresses. We’ll probably never know the whole story of who’s behind this, but we’re getting enough pieces so that we can hobble together a broad picture of what happened.
It appears more and more that the malware caper discovered this weekend on the TOR network was all about harvesting MAC (media access control) addresses. We’ll probably never know the whole story of who’s behind this, but we’re getting enough pieces so that we can hobble together a broad picture of what happened.
When this case first broke, everyone familiar with TOR immediately suspected this had something to do with the hidden child pornography sites that the hacker group Anonymous claimed were being hosted on a TOR hidden services server operated by Freedom Hosting.
That turns out to probably be a correct assumption. According to the Independent, on Friday Eric Eoin Marques, who is allegedly connected with Freedom Hosting, was arrested in Dublin in connection with child pornography charges originating in the U.S.:
“The US authorities are seeking the extradition of a 28 year old Irishman alleged to be involved in the distribution of on-line child pornography and described in the High Court today by an FBI Special Agent as ‘the largest facilitator of child porn on the planet.’
“Twenty-eight-year-old Eric Eoin Marques appeared before Mr Justice Paul Gilligan on foot of an extradition request by the FBI and was today put back in custody until next Thursday.
“The court heard Marques, who has both Irish and US citizenship was arrested on a Maryland, US., warrant that records charges of distributing and promoting child pornography on the internet.”
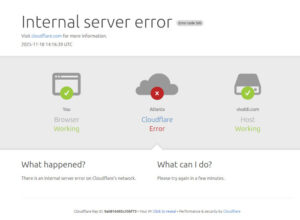
About the same time that Marques was arrested, the hidden services server operated by Freedom Hosting went down. Some time before it went down, however, it was compromised.
NBC tells it this way:
…Before Freedom Hosting went down, it began serving a highly targeted form of malware to all the visitors of the invisible websites it hosted. Not the kind of malware that serves up ads or slows down your computer, but a very specific exploit that caused affected browsers to reveal their own location on the Internet (normally obscured by the Tor network) to a certain IP address.
And who does this IP address appear to belong to? A U.S. defense department security contractor called SAIC, found investigators at Baneki Privacy Labs.
The exploit took advantage of a security hole in Firefox that had already been patched. Unfortunately, however, for the last couple of years users of TOR don’t use their own default browsers but use a forked version of Firefox that’s included in a TOR Browser Bundle that’s downloaded from the TOR website. Sean Michael Kerner wrote a good article explaining why this probably isn’t a good idea which was posted Tuesday on eWeek.
Although the TOR Project’s policies might have left the door open to allow this sort of security breach to happen, that in no way excuses those who took advantage of a situation to execute this exploit. Nor does the fact that the malware installed on TOR users’ computers did no harm other than calling home with an identification report make this any less of a cybercrime. If you leave the door to your house unlocked and I sneak in and merely look around a bit before exiting, I am still guilty of trespassing and breaking and entering, even though I did no harm.
Unless there was a warrant issued allowing this action, it doesn’t even matter if this was part of a federal investigation, which it now appears to have been. Even a cop is breaking the law if he enters your unlocked house to look around.
There are many good reasons why search and seizure regulations were codified centuries ago. Overzealous enforcement of the law is nothing new. Authorities have acted with wanton disregard for citizen’s rights since the beginning of human society. Due process is law our authorities must obey in all circumstances. The constitution doesn’t call for any exceptions. Search and seizure laws aren’t to be followed only if it’s convenient to do so. Nor can they be thrown out the window because the perpetrators are disgusting child abusers.
It’s true the folks who make the decisions at TOR need to reexamine their procedures. What’s more true, however, it that the peoples of the free world need to reexamine the ways and means of those who are paid to protect their freedoms.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux







This was not about CP but about Drugs. I repeat, this was yet another disgrace in the name of the “War on Drugs”. Which if I bite my tongue and call it a “WAR”, I can say that even with the brutal and illegal tactics, the Gov’t got, and keeps getting beat to shit by a bunch of it. Again!
Popular expression needs no protection.
It is the fact that what is perfectly legal today can be made illegal tomorrow on a whim that inspired the idea of “enumerated powers” and “human rights”.
Those who harm children deserve no quarter. Neither do “police” who act as if their supposed “ends” justify any means.
It’s not about child porn _or_ drugs. An attack like this is a psyop more than anything — make people think that Tor can’t be trusted so people won’t use it for anonymous whistleblowing or data sharing that can’t be controlled or monitored by Washington. While taking down the Tor network itself would work for the same aims, it doesn’t have the visual impact of the Freedom Hosting takedown.
The US government is the world’s #1 terrorist.
Without all terrorists, child pornographers etc, the governments will have no excuse for violating human rights in order to keep their power. Am I the only one who thinks that the governments understand this and secretly help their “enemies” where the malicious activities are not strong enough to justify the gov’t HR violations?
I can’t understand why there’s this inherent distrust of our government?…LOL! As if the prisones at GitMo…..the “possibly-must-be-invisible-because-I-never-saw-them” Weapons Of Mass Destruction, the hidden agendas, and other “unknown” happenings that take place on a daily basis, weren’t enough?! As much as I abhor certain criminal acts, i still think ALL men are created “equal” and that we ALL have some inalienable rights! One day, hopefully this world will stop being a refuge for power-mongers, control-freaks, and people who have an uncontrollable NEED to impose their will on others!
What freedoms?! fucnats
If you are one of the little helpless children that terribly abuse and torture by one of those friends of your, would you print that pile of crap – “TOR Case Appears to Be Infringement of Rights”?!
I would shut-down that web-crap permanently and put you in jail!