“Tyranny. Pure and simple. If it is software, somebody will find a way to hack it. If it is hardware, ‘old’ smartphones will be worth their weight in platinum.”
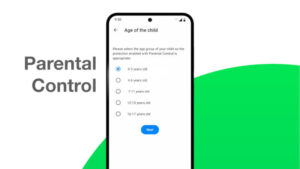
My friend Ross from Toronto made this comment with a link he posted on Facebook to The Free Thought Project’s article on a new about-to-be law in California. The law mandates a kill switch on all new smartphones, allowing the owner of a stolen phone to disable it until it’s recovered. The bill, CA SB 962, now only needs the expected signature of governor Jerry Brown to become law. In July, a similar law went into effect in Minnesota.

Which brings me to Ross’s comment on Facebook. He’s right, of course – or mostly so. Software will be hacked within a day of release, but that’s not what’s important. The meat of his comment is found in a single word, punctuated with a period.
“Tyranny.”
This law is mainly a hoax and will only marginally protect John Q. Public’s phones. Mainly what it does is mandate a door installed on each and every new smartphone that can be used by the police as a tool to quell dissent.
If the owner can disable a phone with nothing but access to a computer or another mobile device, so can Google, Samsung, Microsoft, Nokia or Apple. Google and Apple have already demonstrated their ability to remove software from all devices using their respective operating systems. If the designers of a phone’s operating system can brick a phone, guess who else can do the same? Everybody from the NSA to your friendly neighborhood police force, that’s who. At most, all they’ll need is a convincing argument that they’re acting in the interest of “public safety.”
Before rushing to the conclusion that I’m merely paranoid, consider that in January Prison Planet reported that Google took this Orwellian step:
“Google has filed a patent for identifying when a ‘mob’ event takes place by detecting when a number of cellphone videos or photos are taken at one particular location with the intention of forwarding such information to law enforcement authorities.
“’When there are at least a given number of video clips with similar time stamps and geolocation stamps uploaded to a repository, it is inferred that an event of interest has likely occurred, and a notification signal is transmitted (e.g., to a law enforcement agency, to a news organization, to a publisher of a periodical, to a public blog, etc.),’ states US Patent #20140025755.”
That’s not all. In 2012, Infowars reported that Apple had been granted a patent for a system allowing for the disabling of cameras on all iPhones within a specified location:
“Obviously, the way this will be applied will depend on what is determined to be a ‘sensitive area’ by the relevant authorities.
“To put it bluntly, the powers that be could control what you can and cannot document on your wireless devices according to their own whims.”
Let’s say that the police in Ross’s hometown of Toronto had access to these systems in 2010 during the G-20 summit, when massive police misbehavior was brought to the world’s attention via YouTube. That would have given Toronto’s finest the capability to remotely disable all cell phones, including cameras, within precisely pinpointed areas of the city. Not only would that have greatly hampered protesters ability to organize on-the-fly, it would have shut down the YouTube connection which eventually made the police somewhat publicly accountable.
Or imagine the “Arab spring” protests in Cairo. Those protests would likely have ended quickly, with much bloodshed, had Egyptian President Mubarak had such power at his fingertips.
Unfortunately, it’s not only mobile devices that are under threat. In June, ZDNet said that Intel is working on a RFID-based system that would offer similar control over desktops and laptops:
“The chip giant is working on something call the Wireless Credential Exchange (WCE) with a number of partners. Its chips would communicate with Impinj’s Monza RFID chips to allow remote monitoring of devices via Burnside Digital’s IPTrak software. The result would be that these devices could be controlled to activate only when they reach their approved destination or within a specified location. If they don’t reach their destination or leave the approved area, they could be disabled.”
In this age of militarized police forces, anyone who thinks the police will hesitate to use such capabilities to quell dissent and to hide their illegal behavior is in denial about political reality. The kill switch will not protect a phone from thieves much, if at all, but it will help governments work in darkness.
Ross is right about software, which can be easily thwarted. Workarounds will be posted about as quick as a finger snap after the California law takes effect. Even a hardware implementation will offer little hardship for thieves, as the law requires that disabled phones must be able to be reactivated if and when they are recovered. This would mean some kind of accessible switch, most likely activated by software or firmware.
A kill switch might also give rise to a new type of mobile theft from the black hats. I suspect we’ll soon be reading news of phones going dead except for a message on the screen offering to return control of the device for a payment.
The police, no doubt, will advise against making that payment.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux






The only solution is 100% open software running on 100% open hardware.
Running anything else is to surrender of all your freedom, all your privacy, pure and simple.
Right now, they can just grab all the phones in the viscinity as the Antioch CA Gestapo just did: http://eastcountytoday.net/opinion-tv-media-does-antioch-police-a-disservice-by-going-for-ratings-versus-truths/ Achtung!!
All the new stand-alone cameras have GPS and WiFi. I wonder . . .
/Also, I hate ‘CAPTCHA’ – it never works properly. Never.
Re-read William Gibson’s 1984 novel Neuromancer. Then pick out the bits that are applicable for this day and age. Also note the word microsofts (the ‘s’ is significant). Is that where Bill Gates got it from?
Fascism uses “private” but very large companies with whom they can cooperate to control individuals. The increase in government regulation is to force a small number of companies by driving smaller companies our of business. These large companies get favorable laws and regulations for cooperating with the government. Less regulation allows smaller companies to exist by giving better customer service (and privacy) driving the government co-conspirators out of business.
Less regulation means the companies serve the people rather than the government.
Read “Little Brother” by Cory Doctorow (available for free on Oodles 50000 free books.) He’s snailed this one
Thanks for the citation, Christine! It’s always nice to know somebody gets it.