I recently offered some security tips aimed at new system administrators. And hey, the home users among you should take note, after all, you’re the administrator of your home system! One of the tips was “Don’t run as root.” Today I would like to expand on that a bit. First, we’ll take a look at why you should limit the use of your super powers. Then we’ll look at the best ways to use su and sudo to help you limit your risks.
su or sudo to don your superhero cape when you need to perform system administration tasks. Browsing the web as a regular user is risky. Your regular user account is vulnerable to various malicious attacks. Browsing the web as the root user puts your whole system at risk. Even a simple file deletion as the root user can turn into a disaster if you’re not paying attention.
Remember, the goal here is to reduce your risks. You’ll not likely eliminate all risks, but if you do, please be sure to share your secret. In the meanwhile, though, smart administrators do what they can to reduce the risk of damage to their systems, either through error or attacks. That brings us to su and sudo.
Some libre operating systems prompt you during installation to create a password for the root user, and then to setup a separate, regular user account and password. The idea here is that you login as a regular user, and then use su (Switch User) to gain your super powers. Other systems only ask for a regular user account and password, and then use the sudo utility to let you have such power. openSUSE (and maybe others) lets you choose which way to go at install time. In a single-user environment, you can probably get away with using a root account, but there are cases where you will certainly want to make use of sudo.
Let’s talk about su first. I’ll give some examples with comments to help you understand. For those of you who are new to the command line, the # (hash or bang) symbol is used for one-line comments, typically used in shell scripts, SQL scripts and some programming languages. So when you see that #, everything after it is a comment.
su# with no options, changes your user and group ID, but not much else. You must run exit, or use [Ctrl]+d to return to normal user status.su -# (same as su -l) acts as if you logged in as the root user. This is better than running with no options. As before, you must remember to logout (exit or [Ctrl]+d).su - -c [command]# let’s you run a single command and immediately return to normal user when the command terminates.
If you have a root account, I recommend using this last option as much as possible, as it ensures you won’t remain logged in as root. Let’s look at a couple of examples to help you see how to use it:
su - -c ifconfig# just running a single command, with no options.su - -c "zypper lu"# Note the quote marks – without them, you’ll get an error message to the effect of “user lu does not exist.”
So now you have some practical examples of how to use su to perform system management tasks. Let’s look at how and why you might prefer to use sudo. Some might question the security of sudo, but it does offer some advantages over having a root account, including better control over who can do what, and from what systems. Here are a few advantages:
- Fewer passwords to remember (remember, Keep it Simple, Slick!)
- sudo logs commands run and the users who use (or attempt to use) sudo
- sudo eliminates root account, meaning attackers must figure out which users are admins
- sudo allows you to control who can run which commands, and from which systems
- sudo offers a five-minute timeout (by default), so you can run further sudo commands without re-entering your password. After five minutes, though, you return back to normal privileges and must enter your password again.
Given the above, you can use the sudo logs to trace mistakes and audit your systems. The log should be found under /var/log, but the actual name depends on which system you have installed. Check your sysem’s documentation on this. By limiting what privileged commands admin users can run, and dividing tasks among admins, you can further reduce the risk of damage to your system. It’s just part of a layered approach to security.
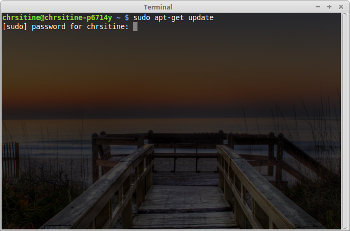
Let’s look at a few examples:
sudo apt-get install [packagename]# runs apt-get to install the specified packagesudo -i# spawns a root shell, so you can run several commands without using sudo every time. However, remember to logout!!!sudo -l# lists which commands you have permission to runsudo -u[username] [command] # let’s you run the specified command with the privileges of another (non-root) user.sudo -e [filename](orsudoedit [filename]) # let’s you edit files that normally require root privileges.
It may be possible to exploit that last option, so you may want to limit what users can run it.
I mentioned that sudo offers greater control over access to privileged system commands. You can use visudo to edit the /etc/sudoers file in order to specify which users (or groups) can run what commands. You can specify what hosts commands can be run from. I won’t go into the specifics of editing your sudoers file here. There are a number of great tutorials out there to help you with that part.
My goal today was to help you better understand the risks of logging in as root, and how to better take advantage of built-in utilities to limit your rootly super powers. If you insist on having a root account, at least make use of the su - -c [command] option. When possible, make the best use of sudo to maintain tight control over access to super powers. Remember, with power comes responsibility. Use your super powers wisely!
Help keep FOSS Force strong. If you like this article, become a subscriber.
Don Parris wears a Facility Services cape by day, and transforms into LibreMan at night. He has written numerous articles about free tech, and hangs out with the Cha-Ha crowd, learning about computer security. He also enjoys making ceviche with his wife, and writing about his travels in Perú.