Cloud computing was always a bad idea.
Not totally bad, mind you. It has its place. I use Google Docs/Drive or whatever they’re calling it this week sometimes so I can work on articles on the computer at my day job without leaving a mess behind on the bosses hard drive. But mostly cloud computing has always been a bad idea.
Ask Richard Stallman; he’ll tell you. Or ask me.
We’ve learned a few things over these last few months, since the truth came out about the NSA. We’ve learned that while we’ve been busy wearing tinfoil hats to keep the government from picking our brains, they’ve been doing it anyway, through our computers, which very well may have been helping them if we’ve been running proprietary software. We’ve learned that if you run Windows you very well might be part of the NSA’s botnet.
Here’s what Paul Venezia who writes for the Data Center at InfoWorld had to say on Monday:
“With the news about PRISM and other clandestine data-vacuuming operations in place all over the world, it’s clear there’s a problem. It’s not just about hoovering up information from millions of people — it’s the vast number of devices that can no longer be trusted for use in business and government. When the code running anywhere along a data path is not open source, there’s a chance it’s doing something you can’t know about and potentially transmitting data to someone who shouldn’t have it. That possibility should serve to upset even nontechnical executives, to say nothing about governments all over the world.”
This is good for us on the penguin farm. It only strengthens our argument that Linux is more secure than the other brands. In Linux, there are no secret back doors. Your computer won’t secretly call it’s handlers at the NSA to file a report on you. If you’re really paranoid and don’t trust the binaries supplied by your distro, afraid they’ve slipped in something nefarious that’s not in the code you’ve seen, go ahead and compile from source. It’ll be a lot of work, but if it makes you sleep better at night, go for it.
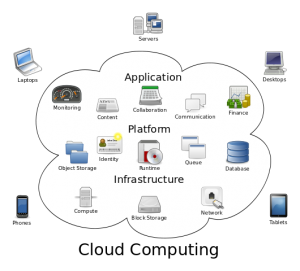 However, when it comes to cloud computing, open source won’t matter, unless it’s your cloud hosted on a server you own and operate. If you’re paying for a cloud service, you might as well go ahead and print up a hard copy of your data to send to the feds in case they ever need it before you upload. You’ll be saving them a lot of work and you won’t have to wonder or worry anymore about whether your data is safe from their eyes.
However, when it comes to cloud computing, open source won’t matter, unless it’s your cloud hosted on a server you own and operate. If you’re paying for a cloud service, you might as well go ahead and print up a hard copy of your data to send to the feds in case they ever need it before you upload. You’ll be saving them a lot of work and you won’t have to wonder or worry anymore about whether your data is safe from their eyes.
Even if it is your cloud, you’re not safe. If we’ve learned anything about the federal government lately, it’s that they know no boundaries. They’re the fox. Your data on your server in the cloud is the hen house. Even encryption won’t help you–not if the fox is really hungry.
Again, Paul Venezia at InfoWorld:
As far as cloud computing goes, that’s outside of the hands of the business and can’t be completely trusted. However, the use of open source encryption can mediate that threat to a degree. But make no mistake — these concerns are only going to make the argument for cloud computing more difficult. As an example, think of how trivial it is to capture data flowing into and out of a cloud server instance at the hypervisor level, straight down into encryption instructions delivered to the virtual CPU.
If you’re an executive type, or an IT manager, you’ve known all along that the cloud isn’t a safe place to store your eggs. That’s why it took so many years for you to warm-up to the idea of the cloud to begin with. Indeed, we are just now getting to the point where cloud computing can be said to be mainstream, as pointed out yesterday by Steven J. Vaughan-Nichols on ZDNet:
“…three out of four companies are moving to the cloud. While the enterprise, at 77-percent, is adopting the cloud faster than SMBs. 73-percent, businesses of all kinds and sizes are embracing cloud computing.”
Now might be the time for businesses and governments to rethink their commitment to cloud computing. Again, it’s not that the cloud is completely a bad idea–it has it’s place and it’s often necessary. However, as with any technology, or technological use, caution must be exercised.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux








Christine: I’ve been preaching this “gospel” since the cloud’s arrival! For some reason I cannot wrap my head around the idea that all of a company’s assets / info / data are available from anywehre on the planet at a moment’s notice. And while in an “Ideal World” that would be a great thing, you have to factor in that if someone can BUILD it….someone else can BREAK it! We’ve seen it time and time again, since the days of Morse Code!…and while it might not be as dramatic as I make it out to be, I can almost FEEL the news headlines coming, of some major global company having all its data that was SUPPOSED to be safe on some cloud farm…stolen, and billions of users names and passwords, along with company records and financial info just evaporating into the same cloud that was supposed to be a safe haven! I mean, I don’t want to sound like some alarmist running around screaming “The Sky Is Falling..!” but for myself, I prefer the safe-ness of a set of 2TB HD’s that hold the data for all of my computers that are backed-up regularly. And while yes, that may place me in the “past” and make me a relic for not adoptiing cloud technology, it’s the safety being compromised I just can’t get past. I have been a Windows Network Administrator since Windows NT 4.0 and I can remember when systems were so “locked down” that if the reigning Admin or Network manager didn’t give you the permissions you didn’t get in,….now it seems that everyone’s rushing to adopt a technology that is so flawed in it’s concept that it makes you wonder what will happen later on and if there will be a way to ever have safe data ever again!
Ha! Anybody who’s been a Windows Network Administrator would have to be utterly paranoid even about two computers in the same internal network talking to each other, no? 😉
Great comment, Eddie.