Breaking News: Patched versions of ImageMagick now available.
FOSS Force has now learned that the ImageTragick hole has been patched in versions 7.0.1-2 and 6.9.4-0. Websites using ImageMagick are urged to upgrade.
Security researchers are reporting that cracker/hackers are currently taking advantage of ImageTragick, the easy to exploit security vulnerability in ImageMagick, a popular open source image manipulation tool used by many websites. However, so far the attacks don’t appear to be widespread.
 FOSS Force first reported on this security bug on May 3. The hole allows an attacker to gain access to a website’s server by uploading a malicious payload disguised as an image file by way of a file name extension. Help Net Security reported today that on Friday the vulnerability was patched in ImageMagick versions 7.0.1-2 and 6.9.4-0.
FOSS Force first reported on this security bug on May 3. The hole allows an attacker to gain access to a website’s server by uploading a malicious payload disguised as an image file by way of a file name extension. Help Net Security reported today that on Friday the vulnerability was patched in ImageMagick versions 7.0.1-2 and 6.9.4-0.
On Saturday, Daniel Cid, founder and CTO of the web security firm Sucuri, posted in a blog in which he said the company was beginning to see attackers attempting to take advantage of the vulnerability. “Interestingly enough,” he wrote, “the attacks themselves seem to be targeted against specific customers and not mass blanket attacks, which is what you’d expect when these type of serious and easy to exploit vulnerabilities are disclosed.”
Part of the reason for this may well be because of the nature of the vulnerability, which requires upload permissions. “These are generally restricted to subscribers and administrators,” Cid notes, “which by design negatively impacts the ability to perform a mass exploit across the web. Additionally, there aren’t that many open-source and public Content Management Systems (CMS) that use ImageMagick by default, which drastically reduces the potential attack surface – something required to see mass attacks.”
While the fact that most CMSes don’t use ImageMagick by default has doubtlessly helped keep exploits of this vulnerability from — excuse us — going viral, there might be a danger that inexperienced bloggers hosting their own sites may be lulled into believing they’re safe when they’re actually at risk, as ImageMagick may still be active on their sites.
For example, the popular WordPress platform, perhaps the most likely to be used by inexperienced users because of its ease of installation and use, doesn’t use ImageMagick by default. However, when FOSS Force took a cursory look at plugins available for the platform, we immediately found seven plugins used by at least 17,000 sites that at least partially replace WordPress’ default image processor with ImageMagick.
Another problem is that even savvy website operators might not know about the ImageTragick vulnerability unless they subscribe to a third party security service or come across an article such as this one on the web. The home page on ImageMagick’s website makes no mention of the vulnerability, not even under a “news” heading, and FOSS Force was only able to find mention of the problem by conducting a site search using the term “security.”
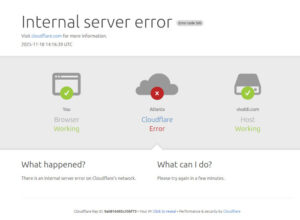
The content delivery network CloudFlare, which is used by FOSS Force, also reports that it’s concerned about the vulnerability and has begun filtering image uploads to the client sites that employ its firewall.
Although current attempts to take advantage of the vulnerability aren’t widespread, Cid cautions website operators using the application against complacency. “[K}nowing there are active attacks should be good reason to update sooner rather than later, especially with the patch process being straight forward.”
Editor’s note: Article was updated Tuesday May 10, 2016 at 2:32 p.m. EDT to include information about availability of patched versions of ImageMagick.