Today I spent some time looking at a white paper issued by the security firm Symantec called Website Security Threat Report, which is basically a catalog of malware threats for the non-techie suits who control the purse strings for web facing server deployments — sort of a “here boss, this is why we have to spend so much money on security” type of thing. Most of it’s old news to those of us who, for whatever reason, follow tech news, but some of the trends noted by the folks at Symantec are interesting enough.
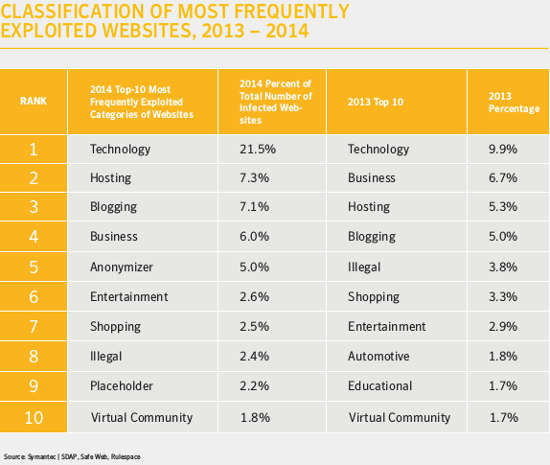
As a matter of fact, there’s a bit of sobering news for sites like FOSS Force, as again in 2014, technology sites top the list of the type of sites most likely to be exploited by cracker hackers, with the number on the rise. According to Symantec, last year tech sites represented 21.5 percent of sites infected by malware, up from 9.9 percent in 2013. Even more disturbing is that number two on this list are hosting sites, up from the number three position in 2013, with 7.3 percent of malware infected sites.
The most interesting part of this paper to me, however, isn’t the mind numbing stats on threats, offered to motivate the suits into spending some money with Symantec — like, last year there were nearly 30 thousand new “malicious web domains,” down 47 percent from a year earlier when the number was over 56 thousand), but the glimpse Symantec offers in a list on page 24, a price list that spells out the wages of cyber crime.
The list illustrates that, as with computer hardware, most areas of cyber crime have become commoditized.
For instance, fifty cents to ten dollars will buy you a thousand stolen email addresses to use for spam or phishing attempts. Do you want to buy some stolen credit cards (hypothetically speaking, of course) to go on an eBay shopping spree? That’ll set you back somewhere between fifty cents to twenty dollars each.
The variety of cyber-stolen goods being offered is also pretty amazing.
You can get a scanned copy of a passport for a dollar or two. Or you can get access to a stolen gaming account so you can buy some virtual weapons or magical powers for ten to fifteen dollars — which seems kinda high to me, but then again I’m not a gamer, so what do I know? Then again, you can get access to a stolen cloud account, evidently so you can fire up a server as a command server for your bots, for seven or eight dollars.

And just like in the legal computing world, the exception to the it’s-all-pretty-cheap-considering rule seems to be when it come to software. If you want someone to design some quality malware for you, that can cost you as much as $3,500. I wonder if the source code comes with that or if it’s some proprietary binary blob? Is it released under the GPL?
Anyway, I find little comfort in knowing that my credit card number will only fetch fifty cents.
Help keep FOSS Force strong. If you like this article, become a subscriber.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux





Cracker hackers. Somehow I’m picturing some good ol’ boy sitting at a keyboard coding away and going “Yeee Haw”!