From Copy Fail to Dirty Frag to Fragnesia and ssh-keysign‑pwn: AI‑driven bug hunters are turning the Linux kernel into a shooting gallery.
Posts published in “Security”
Two kernel zero‑day fixes, two quick Tails releases, and one Tor‑backed project determined to keep its privacy‑minded users safe — this is open source security hygiene in action.
Use-after-free bug in Exim’s GnuTLS BDAT handling lets remote attackers corrupt memory, with no workaround other than upgrading to version 4.99.3.
A trusted Debian dev turns scary new kernel bugs into a temporary one‑click fix until distros ship permanent patches.
‘Copy Fail’ puts Linux users on alert as kernel patches race out and distros scramble to push them to the update channel.
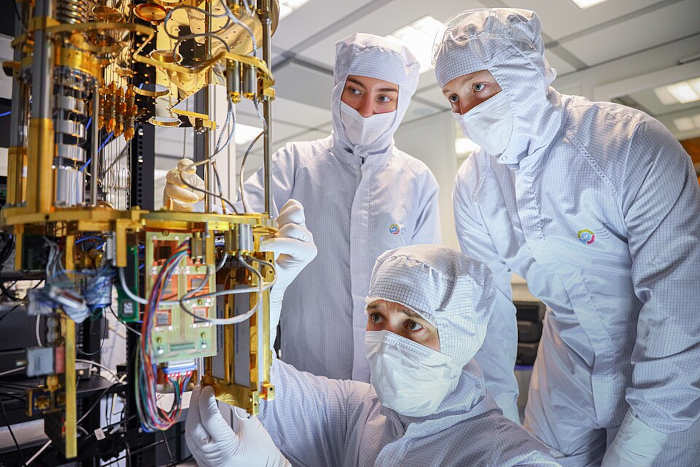
When models can audit firmware and legacy binaries at scale, hiding vulnerabilities stops working. Open, patchable code becomes a core security requirement.
A deterministic password manager that generates, rather than stores, your logins — and makes versioning old passwords surprisingly handy.
We fixed Heartbleed. We didn’t fix the open source funding problem that still asks the people securing our infrastructure to volunteer while we overpay commodity app builders.
Emergency Tails 7.4.1 update patches critical OpenSSL flaws that could let malicious Tor relays deanonymize users.