When models can audit firmware and legacy binaries at scale, hiding vulnerabilities stops working. Open, patchable code becomes a core security requirement.
Posts published in “Security”
A deterministic password manager that generates, rather than stores, your logins — and makes versioning old passwords surprisingly handy.
We fixed Heartbleed. We didn’t fix the open source funding problem that still asks the people securing our infrastructure to volunteer while we overpay commodity app builders.
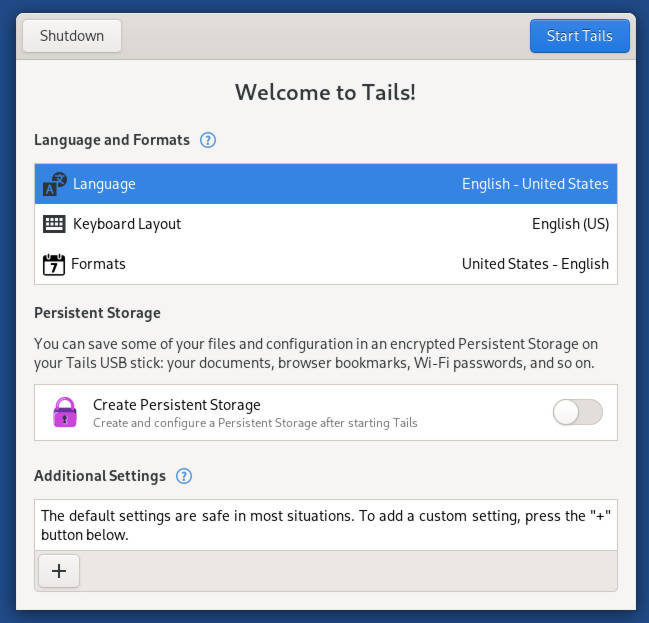
Emergency Tails 7.4.1 update patches critical OpenSSL flaws that could let malicious Tor relays deanonymize users.
Red Hat has quietly bought Chatterbox Labs, a boutique firm that stress‑tests AI models for trouble. Is this a signal that AI safety is moving from marketing slop to production requirement?
Heading into risky online territory? Consider running Tails 7.0, which now offers faster startup and a smoother setup for safer browsing.
TuxCare has added Rocky Linux 9.6 to its 'Enterprise Support' service that had been exclusive to AlmaLinux.
The update from the Arch Linux project says that details of the attack will not be made available as long as it's still ongoing.
Arch’s AUR has been busy battling DDoS attacks and malware. Trouble’s not over—and it’s anybody’s guess what’s next… if anything.