FOSS Week in Review
While Facebook and Google work to better identify you by your typing skills and Red Hat counts the bucks from its best ever year, Ubuntu finally makes it possible to launch from the bottom.
If you depend only on mainstream tech media’s coverage of FOSS, you might be excused for thinking that the biggest news of the week revolved either around Ubuntu’s new summer home in the world of BSD — which isn’t a Canonical project by the way — or Microsoft’s open sourcing of every scrap of code it can find that might benefit Microsoft if it were open sourced.
In my not-so-humble opinion, both of these stories were yawners. Of course somebody’s attempted to create a BSD *buntu. There are already Ubuntu flavors for every single desktop environment known to mankind, as well as a few DEs that are figments of Canonical’s imagination, so where else was there to go but to another operating system? What’s next? Given the way Ubuntu has been cozying up to Microsoft, I’m expecting Ubuntu for Windows.
As for Microsoft’s continuing open sourcing? There’s nothing new here, move on. When Redmond loves Linux and open source enough to quit suing open source projects over patents it claims it has — that will be news.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux


 The case revolves around Verizon’s use of a supercookie — a cookie that uses a variety of techniques to make it nearly impossible to remove or disable — which the carrier began placing on its customers’ phones in 2012. The cookie gathered information that combined a person’s Internet history — whether through browsers or apps — with their unique customer information. The company ran afoul of the law because of the way it shared the information it gleaned with third parties.
The case revolves around Verizon’s use of a supercookie — a cookie that uses a variety of techniques to make it nearly impossible to remove or disable — which the carrier began placing on its customers’ phones in 2012. The cookie gathered information that combined a person’s Internet history — whether through browsers or apps — with their unique customer information. The company ran afoul of the law because of the way it shared the information it gleaned with third parties.





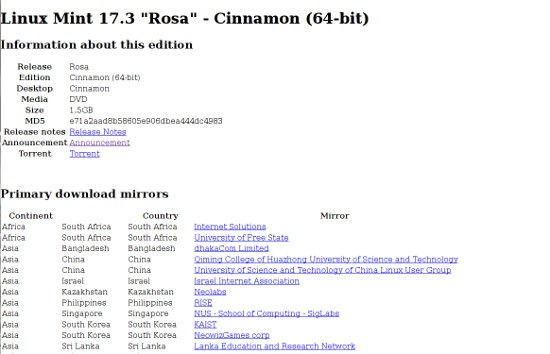
 The Great 2016 Linux Mint Hack: The hack at one of the crown jewels of Linux distros has undoubtedly been the biggest story this week. I’ll not bore you by repeating details which most of you have probably already read by now, but will direct those of you who don’t know to
The Great 2016 Linux Mint Hack: The hack at one of the crown jewels of Linux distros has undoubtedly been the biggest story this week. I’ll not bore you by repeating details which most of you have probably already read by now, but will direct those of you who don’t know to