Today I spent some time looking at a white paper issued by the security firm Symantec called Website Security Threat Report, which is basically a catalog of malware threats for the non-techie suits who control the purse strings for web facing server deployments — sort of a “here boss, this is why we have to spend so much money on security” type of thing. Most of it’s old news to those of us who, for whatever reason, follow tech news, but some of the trends noted by the folks at Symantec are interesting enough.
As a matter of fact, there’s a bit of sobering news for sites like FOSS Force, as again in 2014, technology sites top the list of the type of sites most likely to be exploited by cracker hackers, with the number on the rise. According to Symantec, last year tech sites represented 21.5 percent of sites infected by malware, up from 9.9 percent in 2013. Even more disturbing is that number two on this list are hosting sites, up from the number three position in 2013, with 7.3 percent of malware infected sites.
Christine Hall has been a journalist since 1971. In 2001, she began writing a weekly consumer computer column and started covering Linux and FOSS in 2002 after making the switch to GNU/Linux. Follow her on Twitter: @BrideOfLinux

 We might as well start with the moral of this story: Don’t protect Windows with Windows.
We might as well start with the moral of this story: Don’t protect Windows with Windows.

 Ironically, this side door is intended to be a security door for third party add-ons that every Windows machine needs to keep it safe from cracker hackers — if that’s indeed possible. And this security tool is usually more trusted by Microsoft system admins, especially those outside the U.S., than Windows itself.
Ironically, this side door is intended to be a security door for third party add-ons that every Windows machine needs to keep it safe from cracker hackers — if that’s indeed possible. And this security tool is usually more trusted by Microsoft system admins, especially those outside the U.S., than Windows itself.
 I participate in a group of professional penetration testers (the nice folks who help you test your security as if they were the bad guys) called
I participate in a group of professional penetration testers (the nice folks who help you test your security as if they were the bad guys) called 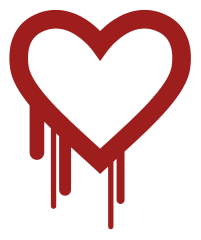
 The neglect he mentions has caused more than a few near misses that fell inches short of disaster, with two major incidents happening last year alone.
The neglect he mentions has caused more than a few near misses that fell inches short of disaster, with two major incidents happening last year alone.
 At the height of the media frenzy that developed around Snowden’s initial revelations, there were allegations that Microsoft had not only built back doors in its software for the NSA and other government agencies to use against foreign businesses and governments, but that it was cooperating with U.S. authorities in other ways as well. For example, one report indicated that the company was passing along details of unpatched security vulnerabilities in Windows to the NSA, effectively adding temporary tools to the spy agency’s cyber arsenal.
At the height of the media frenzy that developed around Snowden’s initial revelations, there were allegations that Microsoft had not only built back doors in its software for the NSA and other government agencies to use against foreign businesses and governments, but that it was cooperating with U.S. authorities in other ways as well. For example, one report indicated that the company was passing along details of unpatched security vulnerabilities in Windows to the NSA, effectively adding temporary tools to the spy agency’s cyber arsenal.